
Why KST Matters
Trust at the Signal Level
Conventional security tools need time to observe, analyze, and decide if something is wrong. But by the time software or specialists detect and confirm a legitimate problem, machine-level attacks have already happened.
Unlike attacks on information systems, attacks on machines — even the machines that create information systems — have real-world consequences. Services can be simply shut down or they could be shattered. People can be hurt or could be broken.
Machines don’t negotiate. They don’t weigh options. They don’t run analytics and you don’t want them to. That isn’t their job. They simply act. A signal arrives, and they respond. It doesn’t matter whether it’s an IT device or an OT device; every machine behaves essentially the same way. If a signal says stop, it stops. Machines must commit the moment the signal hits.
A NAS device stores data where and when it is told. An electromechanical lock opens when the correct keycard is swiped. Electric brakes act the instant a command reaches them.
When you are traveling down a highway with your family you need to know that if the you apply brakes, they apply. If you say release, they release. Brakes shouldn’t consider context or authenticity, they must act — they should. However, this means that if the signal they receive is false, malformed, or spoofed, the brake will still execute it – and therein lies the challenge.
After billions of dollars globally and decades of action to secure our world from emerging cyber threats in the information space, we have made virtually no progress in ensuring the machines that form the foundation of our technologically hyper-connected world can be trusted. Until now.
Blueskytec’s Keyspace Technology (KST) operates at the moment commands appear. It verifies whether the signal is true, real, allowed, correctly formed, and coming from the right source. Because KST is hardware, it can verify trust in that signal in microseconds (millionths of a second). Only legitimate commands reach their destinations.
Machines require real-time proactive protection, not detection. They live too close to the action. Do all the forensics you need if you can, but no one puts the seat belt on during the impact.
KST isn’t just cybersecurity, it’s assured integrity.
Operator Know How
How to deploy KST
01
Choose
Identify Critical Systems and How They Communicate.
Have clear insight to the systems where false signals are unacceptable — where failure will cost lives or destroy operations.
Describe the data pathway requirements for these systems to communicate – protocols, ports, frequency, sizes.
02
Define
Define Allowed Behavior
KST Protectors are endpoint compliance devices. They deny any communication not explicitly allowed.
You define who may talk to whom and in what directions. What frame sizes and timings are allowed. When to encrypt or bypass.
03
Install
Place KST into your Data Pathways
Build a configuration profiles for each KST device, or Blueskytec can do that for you.
Install your factory preconfigured KST Protectors or configure them in-field.
04
Customize
Expand and Scale
Our Private Key process allows you to maintain full authority and flexibility over your installations.
Add Protectors when your needs change.
Federate complex installations with our Gateways.
KST adapts to your needs – not the other way around.

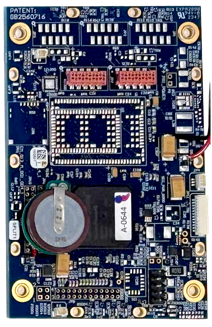
Standard Duty Protector

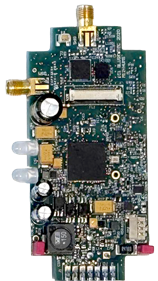
Ruggedized Protector

Redundant Ruggedized Protector

Tracking, Health, Usage and Monitoring (THUM) Protector

Next Step…
✓ Simple Installation
✓ Sophisticated Protection
Keyspace Technology
Single Architecture
Many Applications
M12m
68g / 2.4oz
112mm x 73mm / 4.4in x 2.87in
100ma
M12t
38g / 1.4oz
93mm x 45mm / 3.66in x 1.77in
40ma

M12p
3g / 0.11oz
29mm x 21mm / 1.14in x 0.94in
<1ma

“[KST] addresses a problem we have been trying to solve for over a decade now. And I don’t just mean [our agency], I mean we the ENTIRE PLANET. This has been a big problem that has required a very difficult solution [to develop].”“
U.S. government official with direct responsibility for mission-critical systems
(October 2025)
